- Download Android Apps To PC
Hi folks, one of Techoclock readers named William just asked me a question -  How to download an app from Android Market directly to my PC?I remembered the day when I had the same question and to get an answer I asked this question at several Android forums. I expected the members to come out with a positive answer, but unfortunately NO.
How to download an app from Android Market directly to my PC?I remembered the day when I had the same question and to get an answer I asked this question at several Android forums. I expected the members to come out with a positive answer, but unfortunately NO.There is no way to download Android Market applications directly to your PC using the official Android Market site.
How to Move Android Apps to PC?
In case you wish to store Android apps on your PC, you will have to first download them to your Android device -> Install a backup application ->Backup the apps -> Then transfer them to your PC using Bluetooth or a USB cord.Or if you want to download Android apps on your PC you can read this.How to Download Android Apps to PC?
If your device does not have an internet connection or for some reason you are not able to use Android Market on your device i.e. you are unable to download apps on your device, then there’s a “NOT RECOMMENDED” way of downloading apps first to your PC and then moving them to your Android device and install them.There are innumerable sites that host Android Market applications on their servers. You can download Android apps from these external sources.I don’t recommend using external download sites as you can never trust them. The apps may or may not be tampered, they may contain viruses or worms and they can even be used to hack into your system and leak personal details.I have made a small list of sites hosting Android apps on their servers. Have a look,These sites may not contain all the Android Market apps, but they do have some most popular and useful ones.I recommend using Android Market to download apps if possible and if not use the above sites. Use the sites at your own risk.How To Download APKs Of Android Market Apps To Your Computer With APK Downloader
Certain Android-powered mobile device manufacturers (Amazon and Barnes & Noble, for instance) design their variants of the OS without the Android Market, forcing users to make do with the limited number of apps in their native app stores. You could always install apps of your choice on a Market-sporting Android device, extract their APKs and side-load them onto such devices, but why go through all that trouble when you can use APK Downloader, a Google Chrome extension that lets you download Android Market APKs directly to your desktop. The extension seems to bypass any location or device restrictions, allowing you to easily side-load apps that aren’t yet available for your region, or try out those that are supposedly incompatible with your device. APK Downloader hit the blogosphere a couple of days ago, shortly after which the developer took it down, fearing that it would be used for pirating paid apps. Fortunately, courtesy of the persuasion of a few users, the developer has now released a new version of the extension that only allows downloading free apps.Following is a simple, step-by-step guide to setting up APK Downloader. Don’t be alarmed by the length or quantity of screenshots; the process is pretty straightforward. If you need the extension to side-load Android Market apps onto, say, your Kindle or Nook, you should know that you’ll need the device ID and Google account info of a regular (Gapps-sporting) Android device.1. Launch Chrome, download and install APK Downloader from the developer’s website. An Options form should appear in a new tab right after you click Install.2. If an error asking you to enable SSL error warnings appears above the login form, create a new Google Chrome shortcut, right-click it and select Properties from the context menu (Windows).3. In the Target field, enter a space followed by –ignore-certificate-errors right after chrome.exe. The text at the end should now readchrome.exe --ignore-certificate-errors
4. Once that is done, restart Chrome, this time launching it via the shortcut you just created. The error should now have been removed.5. You should already have the address (Email) and Password of the Google account(s) registered on your Android device. To find out your device’s ID,- Open the dialer (Phone) and enter *#*#8255#*#* to launch GTalk Service Monitor. Scroll down to find the string labeled Device ID. The 16-character string after android- is what you need to enter in the Android Device ID field.
- Alternatively, you may install Device ID from the Android Market. The app displays both the Device ID and the Emails registered on your device.
 6. Hit Login, select a country and mobile carrier from the page that follows, click Save Settings, and you’re good to go.You can now start downloading apps to your computer without even having to log in with your Google account.
6. Hit Login, select a country and mobile carrier from the page that follows, click Save Settings, and you’re good to go.You can now start downloading apps to your computer without even having to log in with your Google account.
 Every time you open an Android app’s Market page, an APK Downloader icon will appear within the URL bar, which you can click to instantly download the app’s APK file to your computer.
Every time you open an Android app’s Market page, an APK Downloader icon will appear within the URL bar, which you can click to instantly download the app’s APK file to your computer. Note: Step 2 is applicable for Windows only.
Note: Step 2 is applicable for Windows only.- Download Paid Apps for Free on Android Market
 Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).
Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).Applanet APK an Alternative Market
Applanet is a site from which you can get paid apps for free. If there are other alternatives such as repositories or Aptoide APKtor, Applanet is the most popular because it is the only notifies you about updates to applications that have installed can update them as if they were the Official Android Market. Remember that you can keep your apps updated following our tutorial: How to keep updated Android applications.Applanet has an interface very similar to the original Market, because the application is based on the code of the Android Market. In addition, Applanet allows you to access the latest versions of more than 14,000 paid Android applications for free as you can find in the Official Market, but with a difference. You will not have to pay for them.This application may also rate and leave comments on the applications you’ve downloaded and installed from Applanet.UPDATE: A little over two weeks reported that the creator was Applanet testing the next version Applanet Ver 3.0. However, as you say multiple users at the moment is not working Applanet. Many say that this application as “dead” although no official details were given about it. Keep you informed with new ads.Download Applanet
To install Applanet must download a reader Bidi, run it and then use the camera to recognize the code. You can also download the APK and once put in the SD, install it with any file manager. Also I leave the Applanet Status Checker, used to check the status of the application Applanet (online or offline).Then I leave some videos that show more detail how to install Applanet video and use this application.- Hacking paid android apps and download free Best Trick
Hello friends, today i am going to share with you how to hack android paid applications and download them absolutely free. By using these tricks and loopholes in android, you will able todownload unlimited android applications and that all absolutely free. Some applications are still not there but you can put a request below and we will try to provide you. This hacking and downloading paid android application involves basic android market that's even only for searching new application names. Basically its not a hack, its just a trick or simply you call it a discovering facts to make our working easier and cheaper.1. Android Market2. Mobile or Iphone should have internet access(optional as i will tell you better alternate way. Why to waste lot of money and data usage on 3G. Use your broadband to download it).3. Phone connectivity to PC or laptop through USB.
How i got idea behind this hack?Normally i use 4shared website to find ebooks and other software's. Yesterday i have download Raging Thunder game on my Samsung Galaxy (android 2.2) and started playing it, as soon as i finished the first level the game has started asking me for purchasing full version. So i started searching on Google to get its full version, but another lol thing happened i founded its full version but we cannot install anything on our mobile from our PC or PC suite(KIES in case of Samsung). So after thinking alot i reached a solutionthat why should not i copy the installer of it onto my memory card of my phone and then try to install it. And guess what happened, it got installed and i really enjoyed full game.
Complete Steps to Hack and download paid android apps for free:1. First of all select which paid android application you want to hack and install its full version for free. I am explaining this article with the help of paid android application Raging Thunder (car racing game).2. Now go to below page and type your android application name then space and then apk in the search box and click on search.
Place where you will find full version of paid android applications
- Download Android Apps To PC
Hi folks, one of Techoclock readers named William just asked me a question -  How to download an app from Android Market directly to my PC?I remembered the day when I had the same question and to get an answer I asked this question at several Android forums. I expected the members to come out with a positive answer, but unfortunately NO.
How to download an app from Android Market directly to my PC?I remembered the day when I had the same question and to get an answer I asked this question at several Android forums. I expected the members to come out with a positive answer, but unfortunately NO.There is no way to download Android Market applications directly to your PC using the official Android Market site.
How to Move Android Apps to PC?
In case you wish to store Android apps on your PC, you will have to first download them to your Android device -> Install a backup application ->Backup the apps -> Then transfer them to your PC using Bluetooth or a USB cord.Or if you want to download Android apps on your PC you can read this.How to Download Android Apps to PC?
If your device does not have an internet connection or for some reason you are not able to use Android Market on your device i.e. you are unable to download apps on your device, then there’s a “NOT RECOMMENDED” way of downloading apps first to your PC and then moving them to your Android device and install them.There are innumerable sites that host Android Market applications on their servers. You can download Android apps from these external sources.I don’t recommend using external download sites as you can never trust them. The apps may or may not be tampered, they may contain viruses or worms and they can even be used to hack into your system and leak personal details.I have made a small list of sites hosting Android apps on their servers. Have a look,These sites may not contain all the Android Market apps, but they do have some most popular and useful ones.I recommend using Android Market to download apps if possible and if not use the above sites. Use the sites at your own risk.How To Download APKs Of Android Market Apps To Your Computer With APK Downloader
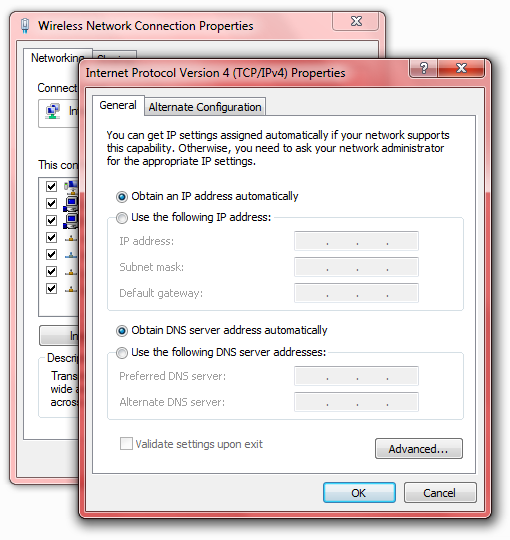
Certain Android-powered mobile device manufacturers (Amazon and Barnes & Noble, for instance) design their variants of the OS without the Android Market, forcing users to make do with the limited number of apps in their native app stores. You could always install apps of your choice on a Market-sporting Android device, extract their APKs and side-load them onto such devices, but why go through all that trouble when you can use APK Downloader, a Google Chrome extension that lets you download Android Market APKs directly to your desktop. The extension seems to bypass any location or device restrictions, allowing you to easily side-load apps that aren’t yet available for your region, or try out those that are supposedly incompatible with your device. APK Downloader hit the blogosphere a couple of days ago, shortly after which the developer took it down, fearing that it would be used for pirating paid apps. Fortunately, courtesy of the persuasion of a few users, the developer has now released a new version of the extension that only allows downloading free apps.Following is a simple, step-by-step guide to setting up APK Downloader. Don’t be alarmed by the length or quantity of screenshots; the process is pretty straightforward. If you need the extension to side-load Android Market apps onto, say, your Kindle or Nook, you should know that you’ll need the device ID and Google account info of a regular (Gapps-sporting) Android device.1. Launch Chrome, download and install APK Downloader from the developer’s website. An Options form should appear in a new tab right after you click Install.2. If an error asking you to enable SSL error warnings appears above the login form, create a new Google Chrome shortcut, right-click it and select Properties from the context menu (Windows).3. In the Target field, enter a space followed by –ignore-certificate-errors right after chrome.exe. The text at the end should now readchrome.exe --ignore-certificate-errors
4. Once that is done, restart Chrome, this time launching it via the shortcut you just created. The error should now have been removed.5. You should already have the address (Email) and Password of the Google account(s) registered on your Android device. To find out your device’s ID,- Open the dialer (Phone) and enter *#*#8255#*#* to launch GTalk Service Monitor. Scroll down to find the string labeled Device ID. The 16-character string after android- is what you need to enter in the Android Device ID field.
- Alternatively, you may install Device ID from the Android Market. The app displays both the Device ID and the Emails registered on your device.
 6. Hit Login, select a country and mobile carrier from the page that follows, click Save Settings, and you’re good to go.You can now start downloading apps to your computer without even having to log in with your Google account.
6. Hit Login, select a country and mobile carrier from the page that follows, click Save Settings, and you’re good to go.You can now start downloading apps to your computer without even having to log in with your Google account.
 Every time you open an Android app’s Market page, an APK Downloader icon will appear within the URL bar, which you can click to instantly download the app’s APK file to your computer.
Every time you open an Android app’s Market page, an APK Downloader icon will appear within the URL bar, which you can click to instantly download the app’s APK file to your computer. Note: Step 2 is applicable for Windows only.
Note: Step 2 is applicable for Windows only.- Download Paid Apps for Free on Android Market
 Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).
Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).Applanet APK an Alternative Market
Applanet is a site from which you can get paid apps for free. If there are other alternatives such as repositories or Aptoide APKtor, Applanet is the most popular because it is the only notifies you about updates to applications that have installed can update them as if they were the Official Android Market. Remember that you can keep your apps updated following our tutorial: How to keep updated Android applications.Applanet has an interface very similar to the original Market, because the application is based on the code of the Android Market. In addition, Applanet allows you to access the latest versions of more than 14,000 paid Android applications for free as you can find in the Official Market, but with a difference. You will not have to pay for them.This application may also rate and leave comments on the applications you’ve downloaded and installed from Applanet.UPDATE: A little over two weeks reported that the creator was Applanet testing the next version Applanet Ver 3.0. However, as you say multiple users at the moment is not working Applanet. Many say that this application as “dead” although no official details were given about it. Keep you informed with new ads.Download Applanet
To install Applanet must download a reader Bidi, run it and then use the camera to recognize the code. You can also download the APK and once put in the SD, install it with any file manager. Also I leave the Applanet Status Checker, used to check the status of the application Applanet (online or offline).Then I leave some videos that show more detail how to install Applanet video and use this application.- Hacking paid android apps and download free Best Trick
Hello friends, today i am going to share with you how to hack android paid applications and download them absolutely free. By using these tricks and loopholes in android, you will able todownload unlimited android applications and that all absolutely free. Some applications are still not there but you can put a request below and we will try to provide you. This hacking and downloading paid android application involves basic android market that's even only for searching new application names. Basically its not a hack, its just a trick or simply you call it a discovering facts to make our working easier and cheaper.1. Android Market2. Mobile or Iphone should have internet access(optional as i will tell you better alternate way. Why to waste lot of money and data usage on 3G. Use your broadband to download it).3. Phone connectivity to PC or laptop through USB.
How i got idea behind this hack?Normally i use 4shared website to find ebooks and other software's. Yesterday i have download Raging Thunder game on my Samsung Galaxy (android 2.2) and started playing it, as soon as i finished the first level the game has started asking me for purchasing full version. So i started searching on Google to get its full version, but another lol thing happened i founded its full version but we cannot install anything on our mobile from our PC or PC suite(KIES in case of Samsung). So after thinking alot i reached a solutionthat why should not i copy the installer of it onto my memory card of my phone and then try to install it. And guess what happened, it got installed and i really enjoyed full game.
Complete Steps to Hack and download paid android apps for free:1. First of all select which paid android application you want to hack and install its full version for free. I am explaining this article with the help of paid android application Raging Thunder (car racing game).2. Now go to below page and type your android application name then space and then apk in the search box and click on search.
Place where you will find full version of paid android applications
- Download Android Apps To PC
Hi folks, one of Techoclock readers named William just asked me a question -  How to download an app from Android Market directly to my PC?I remembered the day when I had the same question and to get an answer I asked this question at several Android forums. I expected the members to come out with a positive answer, but unfortunately NO.
How to download an app from Android Market directly to my PC?I remembered the day when I had the same question and to get an answer I asked this question at several Android forums. I expected the members to come out with a positive answer, but unfortunately NO.There is no way to download Android Market applications directly to your PC using the official Android Market site.
How to Move Android Apps to PC?
In case you wish to store Android apps on your PC, you will have to first download them to your Android device -> Install a backup application ->Backup the apps -> Then transfer them to your PC using Bluetooth or a USB cord.Or if you want to download Android apps on your PC you can read this.How to Download Android Apps to PC?
If your device does not have an internet connection or for some reason you are not able to use Android Market on your device i.e. you are unable to download apps on your device, then there’s a “NOT RECOMMENDED” way of downloading apps first to your PC and then moving them to your Android device and install them.There are innumerable sites that host Android Market applications on their servers. You can download Android apps from these external sources.I don’t recommend using external download sites as you can never trust them. The apps may or may not be tampered, they may contain viruses or worms and they can even be used to hack into your system and leak personal details.I have made a small list of sites hosting Android apps on their servers. Have a look,These sites may not contain all the Android Market apps, but they do have some most popular and useful ones.I recommend using Android Market to download apps if possible and if not use the above sites. Use the sites at your own risk.How To Download APKs Of Android Market Apps To Your Computer With APK Downloader
Certain Android-powered mobile device manufacturers (Amazon and Barnes & Noble, for instance) design their variants of the OS without the Android Market, forcing users to make do with the limited number of apps in their native app stores. You could always install apps of your choice on a Market-sporting Android device, extract their APKs and side-load them onto such devices, but why go through all that trouble when you can use APK Downloader, a Google Chrome extension that lets you download Android Market APKs directly to your desktop. The extension seems to bypass any location or device restrictions, allowing you to easily side-load apps that aren’t yet available for your region, or try out those that are supposedly incompatible with your device. APK Downloader hit the blogosphere a couple of days ago, shortly after which the developer took it down, fearing that it would be used for pirating paid apps. Fortunately, courtesy of the persuasion of a few users, the developer has now released a new version of the extension that only allows downloading free apps.Following is a simple, step-by-step guide to setting up APK Downloader. Don’t be alarmed by the length or quantity of screenshots; the process is pretty straightforward. If you need the extension to side-load Android Market apps onto, say, your Kindle or Nook, you should know that you’ll need the device ID and Google account info of a regular (Gapps-sporting) Android device.1. Launch Chrome, download and install APK Downloader from the developer’s website. An Options form should appear in a new tab right after you click Install.2. If an error asking you to enable SSL error warnings appears above the login form, create a new Google Chrome shortcut, right-click it and select Properties from the context menu (Windows).3. In the Target field, enter a space followed by –ignore-certificate-errors right after chrome.exe. The text at the end should now readchrome.exe --ignore-certificate-errors
4. Once that is done, restart Chrome, this time launching it via the shortcut you just created. The error should now have been removed.5. You should already have the address (Email) and Password of the Google account(s) registered on your Android device. To find out your device’s ID,- Open the dialer (Phone) and enter *#*#8255#*#* to launch GTalk Service Monitor. Scroll down to find the string labeled Device ID. The 16-character string after android- is what you need to enter in the Android Device ID field.
- Alternatively, you may install Device ID from the Android Market. The app displays both the Device ID and the Emails registered on your device.
 6. Hit Login, select a country and mobile carrier from the page that follows, click Save Settings, and you’re good to go.You can now start downloading apps to your computer without even having to log in with your Google account.
6. Hit Login, select a country and mobile carrier from the page that follows, click Save Settings, and you’re good to go.You can now start downloading apps to your computer without even having to log in with your Google account.
 Every time you open an Android app’s Market page, an APK Downloader icon will appear within the URL bar, which you can click to instantly download the app’s APK file to your computer.
Every time you open an Android app’s Market page, an APK Downloader icon will appear within the URL bar, which you can click to instantly download the app’s APK file to your computer. Note: Step 2 is applicable for Windows only.
Note: Step 2 is applicable for Windows only.- Download Paid Apps for Free on Android Market
 Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).
Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).Applanet APK an Alternative Market
Applanet is a site from which you can get paid apps for free. If there are other alternatives such as repositories or Aptoide APKtor, Applanet is the most popular because it is the only notifies you about updates to applications that have installed can update them as if they were the Official Android Market. Remember that you can keep your apps updated following our tutorial: How to keep updated Android applications.Applanet has an interface very similar to the original Market, because the application is based on the code of the Android Market. In addition, Applanet allows you to access the latest versions of more than 14,000 paid Android applications for free as you can find in the Official Market, but with a difference. You will not have to pay for them.This application may also rate and leave comments on the applications you’ve downloaded and installed from Applanet.UPDATE: A little over two weeks reported that the creator was Applanet testing the next version Applanet Ver 3.0. However, as you say multiple users at the moment is not working Applanet. Many say that this application as “dead” although no official details were given about it. Keep you informed with new ads.Download Applanet
To install Applanet must download a reader Bidi, run it and then use the camera to recognize the code. You can also download the APK and once put in the SD, install it with any file manager. Also I leave the Applanet Status Checker, used to check the status of the application Applanet (online or offline).Then I leave some videos that show more detail how to install Applanet video and use this application.- Hacking paid android apps and download free Best Trick
Hello friends, today i am going to share with you how to hack android paid applications and download them absolutely free. By using these tricks and loopholes in android, you will able todownload unlimited android applications and that all absolutely free. Some applications are still not there but you can put a request below and we will try to provide you. This hacking and downloading paid android application involves basic android market that's even only for searching new application names. Basically its not a hack, its just a trick or simply you call it a discovering facts to make our working easier and cheaper.1. Android Market2. Mobile or Iphone should have internet access(optional as i will tell you better alternate way. Why to waste lot of money and data usage on 3G. Use your broadband to download it).3. Phone connectivity to PC or laptop through USB.
How i got idea behind this hack?Normally i use 4shared website to find ebooks and other software's. Yesterday i have download Raging Thunder game on my Samsung Galaxy (android 2.2) and started playing it, as soon as i finished the first level the game has started asking me for purchasing full version. So i started searching on Google to get its full version, but another lol thing happened i founded its full version but we cannot install anything on our mobile from our PC or PC suite(KIES in case of Samsung). So after thinking alot i reached a solutionthat why should not i copy the installer of it onto my memory card of my phone and then try to install it. And guess what happened, it got installed and i really enjoyed full game.
Complete Steps to Hack and download paid android apps for free:1. First of all select which paid android application you want to hack and install its full version for free. I am explaining this article with the help of paid android application Raging Thunder (car racing game).2. Now go to below page and type your android application name then space and then apk in the search box and click on search.
Place where you will find full version of paid android applications
 How to download an app from Android Market directly to my PC?
How to download an app from Android Market directly to my PC?There is no way to download Android Market applications directly to your PC using the official Android Market site.
How to Move Android Apps to PC?
How to Download Android Apps to PC?
How To Download APKs Of Android Market Apps To Your Computer With APK Downloader
chrome.exe --ignore-certificate-errors
- Open the dialer (Phone) and enter *#*#8255#*#* to launch GTalk Service Monitor. Scroll down to find the string labeled Device ID. The 16-character string after android- is what you need to enter in the Android Device ID field.
- Alternatively, you may install Device ID from the Android Market. The app displays both the Device ID and the Emails registered on your device.



- Download Paid Apps for Free on Android Market
 Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).
Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).Applanet APK an Alternative Market
Applanet is a site from which you can get paid apps for free. If there are other alternatives such as repositories or Aptoide APKtor, Applanet is the most popular because it is the only notifies you about updates to applications that have installed can update them as if they were the Official Android Market. Remember that you can keep your apps updated following our tutorial: How to keep updated Android applications.Applanet has an interface very similar to the original Market, because the application is based on the code of the Android Market. In addition, Applanet allows you to access the latest versions of more than 14,000 paid Android applications for free as you can find in the Official Market, but with a difference. You will not have to pay for them.This application may also rate and leave comments on the applications you’ve downloaded and installed from Applanet.UPDATE: A little over two weeks reported that the creator was Applanet testing the next version Applanet Ver 3.0. However, as you say multiple users at the moment is not working Applanet. Many say that this application as “dead” although no official details were given about it. Keep you informed with new ads.Download Applanet
To install Applanet must download a reader Bidi, run it and then use the camera to recognize the code. You can also download the APK and once put in the SD, install it with any file manager. Also I leave the Applanet Status Checker, used to check the status of the application Applanet (online or offline).Then I leave some videos that show more detail how to install Applanet video and use this application.- Hacking paid android apps and download free Best Trick
Hello friends, today i am going to share with you how to hack android paid applications and download them absolutely free. By using these tricks and loopholes in android, you will able todownload unlimited android applications and that all absolutely free. Some applications are still not there but you can put a request below and we will try to provide you. This hacking and downloading paid android application involves basic android market that's even only for searching new application names. Basically its not a hack, its just a trick or simply you call it a discovering facts to make our working easier and cheaper.1. Android Market2. Mobile or Iphone should have internet access(optional as i will tell you better alternate way. Why to waste lot of money and data usage on 3G. Use your broadband to download it).3. Phone connectivity to PC or laptop through USB.
How i got idea behind this hack?Normally i use 4shared website to find ebooks and other software's. Yesterday i have download Raging Thunder game on my Samsung Galaxy (android 2.2) and started playing it, as soon as i finished the first level the game has started asking me for purchasing full version. So i started searching on Google to get its full version, but another lol thing happened i founded its full version but we cannot install anything on our mobile from our PC or PC suite(KIES in case of Samsung). So after thinking alot i reached a solutionthat why should not i copy the installer of it onto my memory card of my phone and then try to install it. And guess what happened, it got installed and i really enjoyed full game.
Complete Steps to Hack and download paid android apps for free:1. First of all select which paid android application you want to hack and install its full version for free. I am explaining this article with the help of paid android application Raging Thunder (car racing game).2. Now go to below page and type your android application name then space and then apk in the search box and click on search.
Place where you will find full version of paid android applications
 Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).
Applanet APK is an alternative that lets you download paid apps for free on Android Market. Here more details of this application, explanatory videos and download links (Android APK).Applanet APK an Alternative Market
Download Applanet
- Hacking paid android apps and download free Best Trick
 |
| Place where you will find full version of paid android applications |